传统防火墙基础实验(1)
6.实现禁止外网访问内网和服务器(除web和telnet服务外)默认已经实现低级别到高级别的流量是拒绝的,如同防火墙默认存在deny所有策略。测试一下访问其他端口和服务。
·
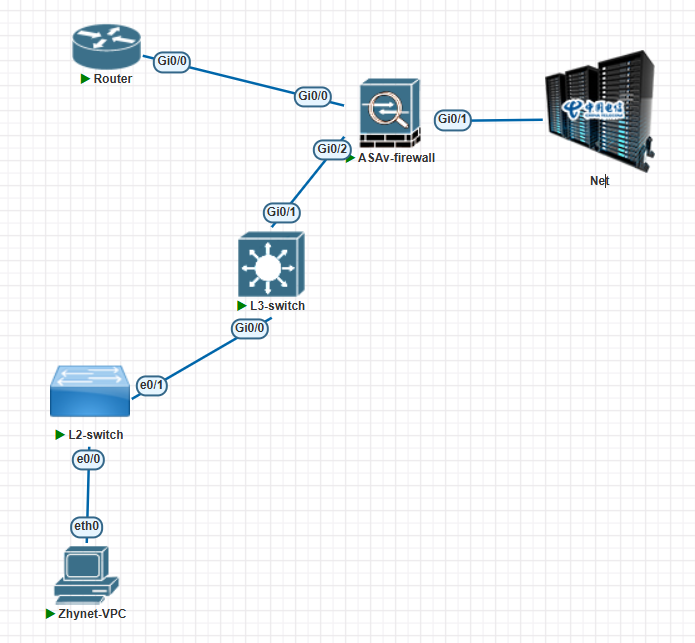
一、实验设备
- Cisco ASA系列防火墙
- 三层交换机一台
- 二层交换机一台
- 路由器一台,用来模拟web服务器
- vpc一台
- 增加一个网络net
二、实验拓扑图
实验目的
- 了解传统防火墙的部署场景
- 理解传统防火墙的包过滤策略
- 了解ASA防火墙的NAT配置
- 理解传统防火墙状态检测的作用
- 理解防火墙的路由模式部署场景
四、实验需求、步骤及配置:
1.vpc配置
Zhynet-VPC> ip 192.168.10.1 255.255.255.0 192.168.10.254
Checking for duplicate address...
Zhynet-VPC : 192.168.10.1 255.255.255.0 gateway 192.168.10.254
Zhynet-VPC> ip dns 114.114.114.114
2.接入层交换机配置
Switch(config)#vlan 10
Switch(config-vlan)#exit
Switch(config)#interface e0/0
Switch(config-if)#switchport mode access
Switch(config-if)#switchport access vlan 10
Switch(config-if)#exit
Switch(config)#interface e0/1
Switch(config-if)#switchport trunk encapsulation dot1q
Switch(config-if)#switchport mode trunk
3.核心/汇聚层交换机配置
Switch(config)#vlan 10
Switch(config-vlan)#exit
Switch(config)#interface g0/0
Switch(config-if)#switchport trunk encapsulation dot1q
Switch(config-if)#switchport mode trunk
Switch(config-if)#exit
Switch(config)#ip routing //启动路由功能
Switch(config)#interface vlan 10
Switch(config-if)#ip address 192.168.10.254 255.255.255.0
Switch(config-if)#no shutdown
Switch(config)#interface g0/1
Switch(config-if)#no switchport //改为三层接口
Switch(config-if)#ip address 10.1.1.1 255.255.255.252
Switch(config)#ip route 0.0.0.0 0.0.0.0 10.1.1.2 //配置上网的缺省路由,下一跳为防火墙接口g0/2
4.服务器区配置
Router(config)#interface g0/0
Router(config-if)#ip address 192.168.2.88 255.255.255.0
Router(config-if)#no shutdown
Router(config-if)#no ip routing //关闭路由功能,模拟一台服务器主机
Router(config)#ip default-gateway 192.168.2.1 //给主机配置默认网关指向防火墙g0/0
Router(config)#ip name-server 114.114.114.114//给主机配置dns服务器
Router(config)#ip http server //开启80端口
Router(config)#line vty 0 4 //开启telnet服务做配置,即23端口服务
Router(config-line)#no login
Router(config-line)#transport input telnet
Router(config-line)#exit
5.公网边界区,ASA防火墙配置
1.基本配置,划分三个安全区域:
ciscoasa(config)# interface g0/2
ciscoasa(config-if)# nameif inside //定义内网区域名 并绑定端口g0/2口
INFO: Security level for "inside" set to 100 by default.
ciscoasa(config-if)# security-level 100 //定义安全级别(类似书写ACL:默认高级别区域可以访问低级别区域)
ciscoasa(config-if)# ip address 10.1.1.2 255.255.255.252
ciscoasa(config-if)# no shutdown
ciscoasa(config-if)# exit
ciscoasa(config)# interface g0/1
ciscoasa(config-if)# nameif outside //公网区域
INFO: Security level for "outside" set to 0 by default.
ciscoasa(config-if)# security-level 0
ciscoasa(config-if)# ip address dhcp setroute //配置为dhcp客户端,从net网络获取IP,并获得默认路由。
ciscoasa(config-if)# no shutdown
ciscoasa(config-if)# exit
ciscoasa(config)# interface g0/0
ciscoasa(config-if)# no shutdown
ciscoasa(config-if)# nameif dmz /服务器区域
INFO: Security level for "dmz" set to 0 by default.
ciscoasa(config-if)# security-level 50
ciscoasa(config-if)# ip address 192.168.2.1 255.255.255.0
ciscoasa(config-if)# exit
ciscoasa(config)# exit
ciscoasa# show interface ip brief //查看各接口IP,包括dhcp获得的
Interface IP-Address OK? Method Status Protocol
GigabitEthernet0/0 192.168.2.1 YES manual up up
GigabitEthernet0/1 192.168.38.150 YES DHCP up up
GigabitEthernet0/2 10.1.1.2 YES manual up up
GigabitEthernet0/3 unassigned YES unset administratively down down
GigabitEthernet0/4 unassigned YES unset administratively down down
GigabitEthernet0/5 unassigned YES unset administratively down down
GigabitEthernet0/6 unassigned YES unset administratively down down
Management0/0 unassigned YES unset administratively down down
2.防火墙路由配置:
ciscoasa(config)# route inside 192.168.10.0 255.255.255.0 10.1.1.1
ciscoasa(config)# show route
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
Gateway of last resort is 192.168.38.2 to network 0.0.0.0
S* 0.0.0.0 0.0.0.0 [1/0] via 192.168.38.2, outside
C 10.1.1.0 255.255.255.252 is directly connected, inside
L 10.1.1.2 255.255.255.255 is directly connected, inside
C 192.168.2.0 255.255.255.0 is directly connected, dmz
L 192.168.2.1 255.255.255.255 is directly connected, dmz
S 192.168.10.0 255.255.255.0 [1/0] via 10.1.1.1, inside
C 192.168.38.0 255.255.255.0 is directly connected, outside
L 192.168.38.150 255.255.255.255 is directly connected, outside
3.实现内网vpc可以上公网,使用动态NAT及配置:
ASA防火墙默认不对ICMP做状态检测,需开启ICMP状态检测,TCP/UDP默认做状态检测。
ciscoasa(config)# object network inside
ciscoasa(config-network-object)# subnet 192.168.10.0 255.255.255.0
ciscoasa(config-network-object)# exit
ciscoasa(config)# object network outside-pool
ciscoasa(config-network-object)# range 192.168.38.151 192.168.38.152
ciscoasa(config-network-object)# exit
ciscoasa(config)# object network inside
ciscoasa(config-network-object)# nat dynamic outside-pool
ciscoasa(config-network-object)# exit
ciscoasa(config)# policy-map global_policy
ciscoasa(config-pmap)# class inspection_default
ciscoasa(config-pmap-c)# inspect icmp
ciscoasa(config-pmap-c)# exit
PC可以访问外网: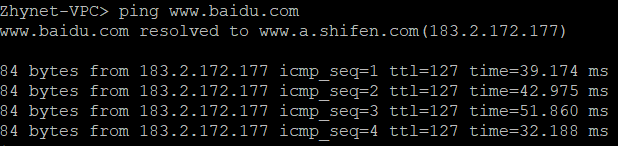
4.实现服务器区中服务器Router可以上公网,以便升级病毒库:
ciscoasa(config)# object network dmz
ciscoasa(config-network-object)# subnet 192.168.2.0 255.255.255.0
ciscoasa(config-network-object)# nat (dmz,outside) dynamic interface //用outside接口IP做PAT
5.实现服务器区中服务器对外提供TCP 80端口web服务和TCP 23端口telnet服务,使用静态NAT及配置:
ciscoasa(config)# object network dmz1
ciscoasa(config-network-object)# host 192.168.2.88
ciscoasa(config-network-object)# nat (dmz,outside) static 192.168.38.153 service tcp 23 23 //前23代表内部服务器的开放端口,后23代表外部用户访问的端口,也可以和内部开放的端口不一样
ciscoasa(config)# object network dmz2
ciscoasa(config-network-object)# host 192.168.2.88
ciscoasa(config-network-object)# nat (dmz,outside) static 192.168.38.154 service tcp 80 80
//防火墙默认不允许从低级别区域向高级别区域发起连接,则需要手工放通即ACL放行进来的流量(放行outside区域访问dmz区域流量)
ciscoasa(config)# access-list webtel permit tcp any host 192.168.2.88 eq 80
ciscoasa(config)# access-list webtel permit tcp any host 192.168.2.88 eq 23
ciscoasa(config)# access-group webtel in interface outside
防火墙配置如下: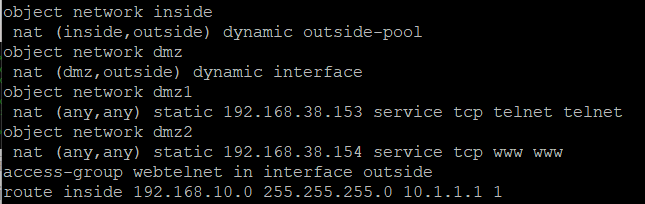
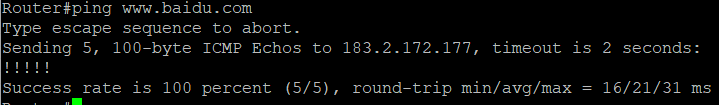
在物理PC机上可以进行telnet: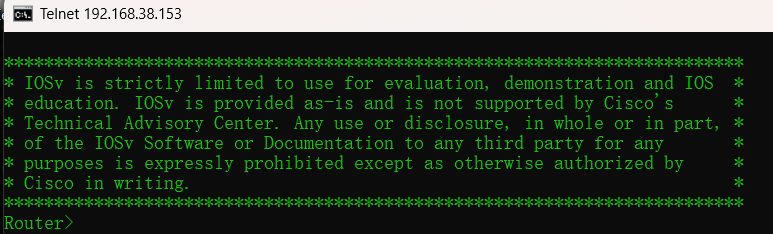
6.实现禁止外网访问内网和服务器(除web和telnet服务外)默认已经实现低级别到高级别的流量是拒绝的,如同防火墙默认存在deny所有策略。测试一下访问其他端口和服务。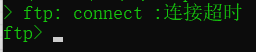
更多推荐
 已为社区贡献2条内容
已为社区贡献2条内容






所有评论(0)